The History of Access Control
Welcome to our blog series on the history of electronic security, where we aim to share and showcase the security industry over a number of informative blog posts. This week we travel back to the time of the pharaohs to discover the origins of Access Control and the history behind it.
As a leading specialist, installing Integrated Security Systems for more than 18 years, we are beginning to see a major change in the security industry. Many people think that the security systems we use now, are very technically advanced. Here at Monatrix we believe there are exciting and significant advancements emerging within the security industry and we are championing these advancements.
New and creative ‘AI’ developments allows systems to assist in the management of day-to-day life and it isn’t a case of IF but WHEN ‘Cloud Based’ systems replace on-premises, ‘On Prem’ solutions.
But before we discuss AI or what these cloud-based systems can do and where is it all going, it made us think about where it all started and the history of electronic security.
Access Control is believed to have started approximately 6000 years ago with Egyptian locking systems and wooden pin locks, then developing into metal locks and keys. Much like us today, the Egyptians designed these systems to protect belongings and places of religious significance.
Fast forward to the 20th century the need for improved security was required to control who went where, keys and locks were replaced by the invention of the pushbutton coded lock in the 1960s and in the 1980’s the electronic versions, with usually 4–6-digit codes, were introduced.
The obvious flaw with these locks was that if an individual witnessed you inputting the code, the security of the area/room had now been compromised. Furthermore, if the codes were not changed regularly then again, the control of who could enter was lost.
Card Readers were invented in the 1970s, but these were for ‘punch cards’ that had punch holes in the card. These systems became prevalent in hotels, but the cards were disposed of after each guest use, as they could not be re-coded. Bar Code cards came next, but these were soon replaced in the 1980s by ‘Electrified Magstripe’ cards.
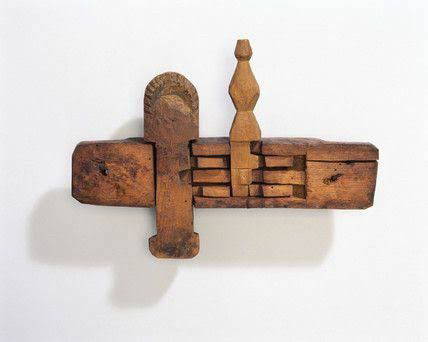
Approx. 6000 year old Egyptian locking systems
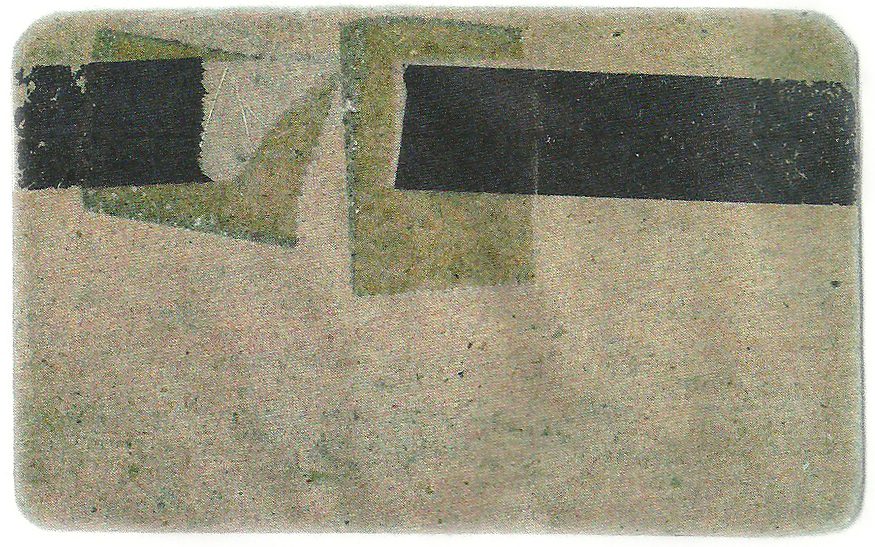
The first prototype of magnetic stripe card created by IBM in the late 1960’s. A stripe of cellophane magnetic tape is fixed to a piece of cardboard with clear adhesive tape. This invention would then push magnetic strip cards to the forefront of access control in the beginning of the 21st Century.
By Jerome Svigals, CC BY 3.0, https://commons.wikimedia.org/w/index.php?curid=20149452
The Magstripe card had been invented in the 1960s for data storage, like account information as a credit card but the unique ‘Key’ storage ability of the card wasn’t realised for another 20 years when Tor Sornes based in Norway offered a new Magstripe access control card that could be re-coded. The basis of todays’ Electronic Access Control had arrived, and readers began to be connected to door controllers, who were configured by a database of credentials, the user’s keys.
This now allowed systems to control who went where and when and stored the information for reporting. The introduction of the internet in the 1990’s also allowed door controllers in remote buildings, to communicate with the same database. So, card users could use the same card all around the world.
In the 1990s RFID (Radio Frequency Identification) used electronic waves to communicate with the card readers and made the cards known as proximity cards. RFID card technologies are predominantly used nowadays but Biometrics have been about for some time as well. Biometrics mean that you do not have to carry a ‘key’ of any kind as YOU are the key.
Despite their frequent use in movies such as Mission Impossible and James Bond. Hand scanners, which were originally used in the 1980s could be too easily fooled, therefore they were not a secure option.
Iris, face and finger scanners appeared in the 1990s but again could be fooled, are expensive and generally not capable of being used externally, which means they cannot be used for perimeter doors. There may also be a reluctance from people to use these devices, due to privacy concerns and the possibility of germ transference.
Biometrics Technologies have advanced a long way in the last 20 years and incorporating AI will mean that voice and facial recognition will play a major part in the future of access control. As will mobile credential technology and ‘Cloud Based’ software platforms and databases.
So, I think you’ll agree, a lot has happened in 6000 years.

Mission Impossible: Rogue Nation (2015)